If you've ever looked at a lake before when the sun is somewhat low, you'll notice that there's glare, and it's hard to see below the surface. Light from the sun bounces off the water, and the ones that create the glare are "propagating" in the horizontal direction (in incoherent light, which comes from the sun, they're propagating in every direction).
By "propagating," I mean you can imagine it as a sine wave that's moving along some axis. So horizontally-polarized light is moving left-right-left-right-left-right really really fast. (That's not what's actually happening but go with it! It works for our analogy).
Suppose you're wearing shutter shades, like the ones Obama is wearing:
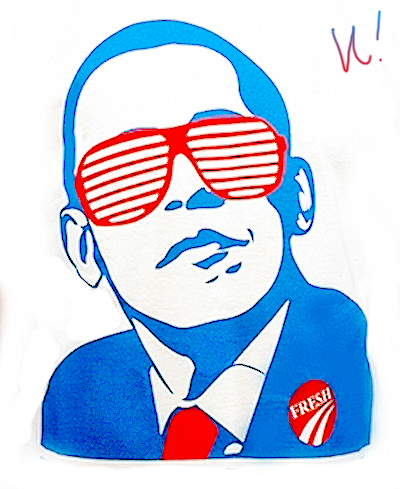 |
| (Not my art! Please don't sue me.) |
What if you take a pair of sunglasses, and turn it 90 degrees? Now you have a vertically-polarized filter, that only lets in vertical light, and blocks out horizontal light. If you take both of these sunglasses and put them one in front of the other, what happens?
Light hits the horizontally-polarized filter, horizontal light goes through. Horizontal light hits the vertically-polarized filter, nothing gets through.
(This is an experiment that you can and should do, by the way. Find a Walgreens somewhere and try this).
Now, what if you put another filter, but rotated it 45 degrees? So you have a horizontal filter, a 45 degree filter, and a vertical filter, in front of each other. What happens?
The sensible thing to say is, well! Filters only block light! So if you take the configuration with the horizontal filter + the vertical filter, and you get no light, then doing the horizontal + 45 + vertical should also get no light!
But that's not what actually happens. You actually get 12.5% of the light you put in.
WHAT.
Somehow, putting an extra filter in the apparatus managed to create light, even though filters only block. More accurately, the 45-degree filter actually destroyed some information about the horizontal filter.
I'm going to allude to the punch line early, this is the same sort of mechanism at play behind Heisenberg's uncertainty principle. Some properties can't be successfully measured at the same time. With Heisenberg, it's position and momentum. With sunglasses, it's propagation direction between two axes.
What if you had five sunglasses instead? One horizontal, one at 22.5 degrees, one at 45 degrees, one at 67.5 degrees, then one vertical? You get more light. The more filters you put in in this manner, the less light that is actually filtered out.
If you have an infinite number of filters, all a tiny angle away from each other, such that you start from the horizontal and end up at the vertical, you actually end up getting 100% of the light going through, as if you had no filters at all.
Clearly this is some demented stuff, and as far as I know, no one fully understands it. We're good at modeling it, but not explaining it in any satisfactory, classical way.
Some extra thoughts:
Let's go back to two filters: one at horizontal and one at 45 degrees. If you send in 100 photons of light, and all 100 get through the horizontal filter, 50 of those get through the 45 degree filter. But which 50?
Let's send in one photon. It gets through half of the time, and half of the time not. Same experiment, different results. There must be some variable we aren't taking into account; the photons that we are preparing, which we think are identical, must not be in some way. No one has found such a variable.
So as far as we know, setting up the same experiment does not always yield the same result.
This is the Copenhagen interpretation: science is not perfectly deterministic, as we thought it'd be.
Einstein hated this. He famously stated that "God does not play dice," and that quantum mechanics must be incomplete. But almost every experiment we've run seems to reinforce the Copenhagen interpretation.
Contrary to what some philosophers thought, this hasn't destroyed science. We're perfectly capable of designing things such that the probability of crazy things happening is very, very, very small. So it's not a big deal, yo.


